In this blog, we will give you a simple and clear explanation of each types of rootkits so that it will be easy for you to understand better.
Computer users may see the term “rootkit” that relates to viruses or attacks on devices, as well as malware – and for a good reason. Besides being dangerous, rootkits are incredibly clever – you won’t even realize that you have them on your computer. Many people are unaware that such a threat exists and may be infected.
‘Rootkit’ is a software kit that allows one to reach the root of a computer. In simple language, a software kit gives the administrator access to the computer and thus gives them control. The software program was developed as a fair solution to provide software developers with a ‘backdoor’ to fix issues with their products – but today, unfortunately, it is manipulated by hackers to gain access to weak computers and steal their data.
In this blog, we will be going to discuss the types of rootkits. So let’s get started.
What is a rootkit?
Table of Contents
A rootkit can be defined as a combination of “root” and “putty”. The Unix system calls itself “root”, which refers to the user with full, unrestricted access to the system. Putty refers to a collection of tools and programs. This combination of words signifies the threat of hazardous software that can be installed on a computer to grant a hacker remote and permanent access to it to install various tools. The purpose of these programs is typically to steal data, and the user is usually unaware that his device has been compromised. Therefore, the threat posed by rootkits is not to be taken lightly.
Like keyloggers, rootkits avoid detection by nesting as deep within the system as possible and cleverly avoiding detection by antivirus programs. Cybercriminals can use it to install additional components in the victim’s system and remove them. The most familiar tools in rootkits are:
- Theft modules blocked passwords, credit card numbers, and online banking information.
- Bots for DDoS assaults
- Keyloggers (mechanisms for recording keystrokes on a keyboard);
- Security systems can be circumvented and disabled using functions capable of bypassing and disabling security systems.
Origin of rootkit
The first malicious rootkit for the Windows NT operating system occurred in 1999: a trojan called NTRootkit created by Greg Hoglund. HackerDefender followed it in 2003. The first rootkit targeting Mac OS X occurred in 2009, while the Stuxnet worm was the first to target programmable logic controllers (PLC).
Different types of rootkits
Below we are going to discuss different types of rootkits:
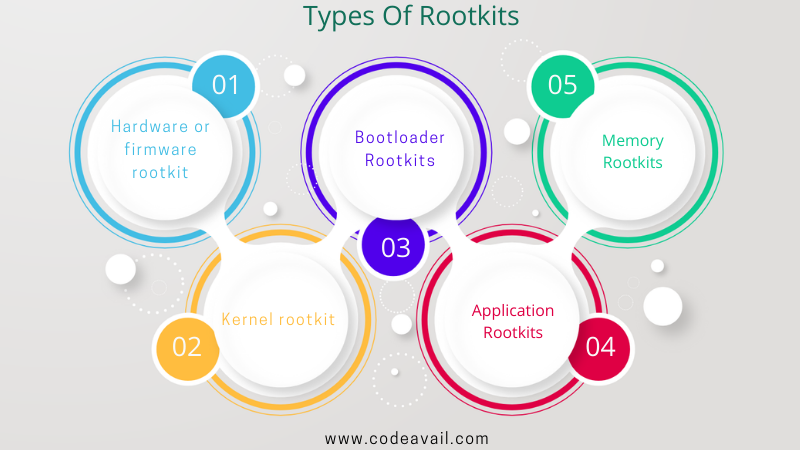
Hardware or firmware rootkit
Hardware or firmware rootkits are less common than other types, but they still pose a serious threat to internet security. These rootkits can damage your hard drive, router, or BIOS, which is the software installed on your computer’s motherboard. Rather than targeting your operating system, they target your device’s firmware to install malware that is difficult to detect. In addition to logging keystrokes, they can also monitor online activity since they affect hardware.
Kernel rootkit
Kernel-mode rootkits are among the most dangerous forms of this threat since they attack the kernel level of your operating system. By adding their own code, hackers can access the files on your computer and modify the functionality of your operating system.
Bootloader rootkits
Your computer’s operating system isn’t fully loaded when you activate the rootkit. In most computers, the bootloader mechanism is responsible for loading the operating system. Hackers use bootloader rootkits to replace your computer’s legitimate bootloader with a hacked one.
Application rootkits
A rootkit replaces your computer’s standard files with its own files, and in some cases, can even change how the applications work. Rootkits can infect programs like Microsoft Office, Notepad, or Paint. If you run these programs, an attacker can access your computer. Rootkit detection is difficult for users to detect since infected programs are running normally – but antivirus software can detect them since they both operate at the application layer.
Memory rootkits
The memory rootkit hides in your computer’s random-access memory (RAM) and uses the computer’s resources to carry out malicious activities in the background. These rootkits affect the performance of your computer’s RAM. Because memory rootkits only run in your computer’s RAM and don’t inject permanent code. They disappear as soon as the computer reboots – though sometimes further efforts are necessary to eradicate them. Their short lifespan makes them less of a threat.
| Also, check details on what are the security risks of cloud computing |
How to detect rootkits?
Now you know the types of rootkits. Let’s see how to detect rootkits. As rootkits are specifically designed to remain hidden, detecting their presence on a computer can be difficult. Furthermore, rootkits can disable security software, making the task even more difficult. Because of this, rootkit malware could remain on your computer for quite a while and cause significant damage.
Possible signs of rootkit malware include:
Blue screen
Blue screens with white text or error messages are frequent (also referred to as “the blue screen of death”) while your computer constantly needs to reboot.
Unusual web browser behaviour
Unrecognized bookmarks and redirections might be involved.
Slow device performance
You may find that your device takes a long time to start and performs slowly or freezes frequently. The device might also not respond to input from the mouse or keyboard.
Windows settings change without permission
The screensaver might change, the taskbar might disappear, or the date and time might display incorrectly – when you haven’t changed anything.
Web pages don’t function properly
Excessive network traffic results in intermittent web pages or network activity that does not function properly.
The best way to detect a rootkit infection is to perform a rootkit scan, which your antivirus solution can perform. An easy way to detect a rootkit virus is to shut down the computer and run the scan from a known clean system.
Behavioral analysis is another method of detecting rootkits. Instead of looking for the rootkit, you look for rootkit-like behaviors. In contrast to targeted scans, a behavioral analysis may detect a rootkit before you are aware you are under attack.
How to prevent a rootkit infection?
Rootkits may be problematic and constant, but at last, it is just a program like different types of malware. It indicates that they only damage your computer after running the malicious program that bears the rootkit.
Here are some measures to prevent you from being affected by rootkits and bypass all the time-consuming steps.
Keep your software updated at all times
If your software is outdated and not up to date on time, this is the main reason for malware infection. All human creation and software programs are not perfect. They come up with many bugs and problems. These problems allow hackers to exploit these programs.
To protect yourself from malicious hackers and malware, you should keep your software up to date at all times.
Well, updating the software all the time is a very tricky task. You can try our Heimdal™ Patch & Asset Management designed to handle such situations. We recommend you utilize our auto-updated program for you.
Be wary of phishing or spear-phishing attempts
Phishing is a social engineering attack in which scammers send emails to trick users into providing their financial information or downloading malicious software. Do not open suspicious emails, especially from unknown senders, to avoid rootkit infections. If you’re unsure if a link is trustworthy, don’t click on it.
Download files from trusted sources only
Open attachments carefully and do not open attachments from unknown senders to avoid installing rootkits. Make sure you download software only from reputable sources. Please do not ignore your web browser’s warnings when it tells you a website you are trying to access is unsafe.
Final words
In this blog, we have mentioned different types of rootkits and included how to detect rootkits in the operating system and give proper knowledge about How to prevent a rootkit infection. We hope that our blog will become very useful for you and clear all your doubts regarding types of rootkits. If you are a student and facing difficulty regarding Computer Network Homework Help. Our experts will provide you with the best Computer Network Homework Help at an affordable price.
Is rootkit is a type of malware?
A rootkit is a type of software that allows hackers to access and control a target device. Although most rootkits attack software and the operating system, some can also infect the hardware and firmware of your machine.
What are the two types of rootkits?
User-mode or application rootkit: These are installed in a shared library and operate at the application layer to modify application and API behavior.
Kernel-mode: These rootkits are implemented within an operating system’s kernel module to handle all processes.